Proprietary close source backend? No thanks
Then use opensnitch
Thanks for the recommendation. However, the UI of this proprietary app does look nice.
The first paragraph is kind of ironic considering this is closed source software.
Lately, there’s been a growing unease around software, and not just among security folks. With governments and big organizations starting to rethink their reliance on foreign-controlled tech, a pretty uncomfortable truth is getting more attention. If a vendor controls updates, it can push whatever code it wants onto your machine, whenever it wants, with full privileges. Most people know this on some level, but it’s easier not to dwell on it.
Software that listens to every internet connection on your PC has the potential to be pretty invasive if it’a malicious.
I use little snitch on my Mac. I’ve always hated how it wasn’t available for Linux. I understand that some people don’t like proprietary software, but there have been no cases of anyone suggesting this developer is untrustworthy. I know that’s a gamble, but even with open source software… Is anyone Actually looking through that code themselves? No.
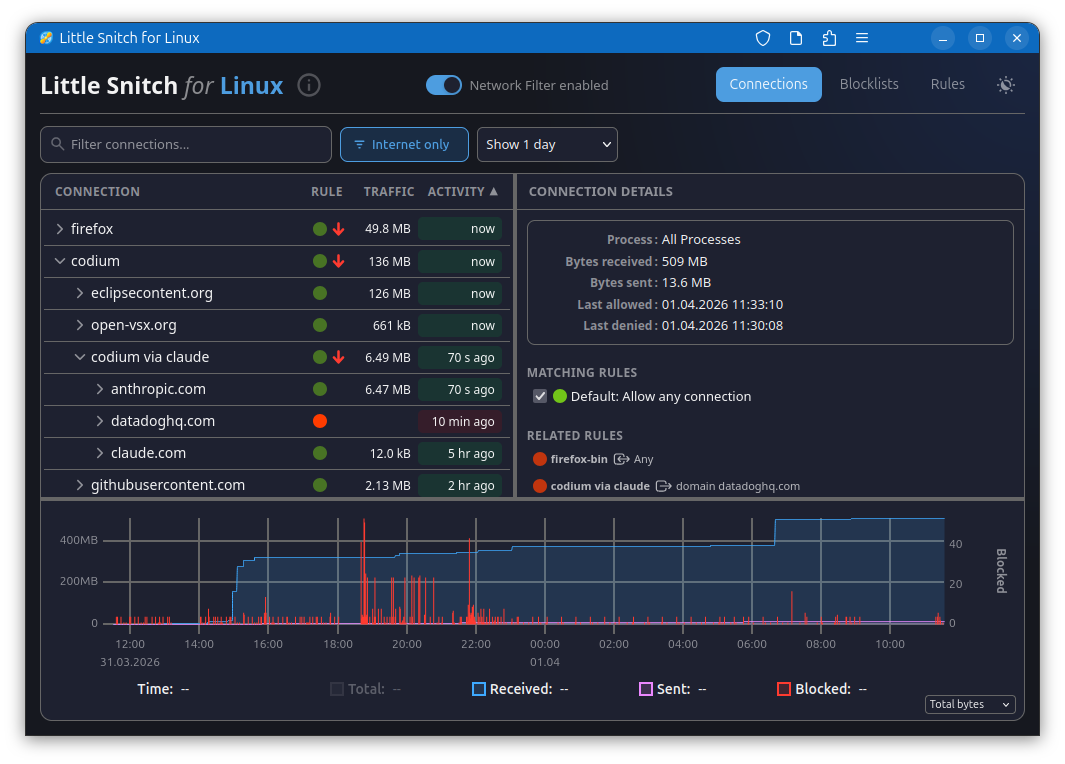
Having the software installed has pointed out how many applications actually ask for an Internet connection. It tells you exactly where they’re going, And you can block specific domains and IP addresses from specific applications. It gets very fine grain.
Anyway, I like it and I think everybody should be running at least open snitch.
For a FOSS enthusiast, this is a total non-starter. We don’t migrate to Linux just to swap one proprietary black box for another. If I cannot audit the code that sits between my binaries and the internet, I am not interested.
That’s hardcore. Are there any network cards with fully open firmware? How does one learn to audit code for how many layers there are to this? Does this person has time for anything other than auditing code? Or is this and other claims a satire?
True “open source firmware” where you can inspect and modify everything on a network card is going to be rare if they exist. However, Linux has mature open source drivers that interface with the hardware for consideration and the output can be monitored at a gateway/router.
These strawman arguements aside, I think the author’s point is that the purpose of this tool is for privacy of network connections and as such deserves scrutiny.
To your point, open source does not equal secure. We still have to trust that someone more familiar and with interest has reviewed the code and humans can still err.
The author provides links to an open solution that has already existed (albeit not as polished) and explains his other solution blocking at a DNS level.
The problem with a black box network monitoring and blocking solution is we have no clue if there are rules we are unaware of or if all information is being provided in earnest. Ultimately this tool is hosted by a business selling other privacy conscious applications. I know If you’re good at what you do, don’t give it away for free.
Ultimately, everyone is free to choose their own solution but the article cautions of the hype that’s emerging around this tool when other solutions have existed that are more transparent.
https://safing.io/ Already Foss
Neat, I thought this one was Windows-only.
Is there any comprehensive comparison with opensnitch?
Pihole has similar functionality, and it’s FOSS.
simplewall for windows https://github.com/henrypp/simplewall