By Bertel King - Published Apr 22, 2026
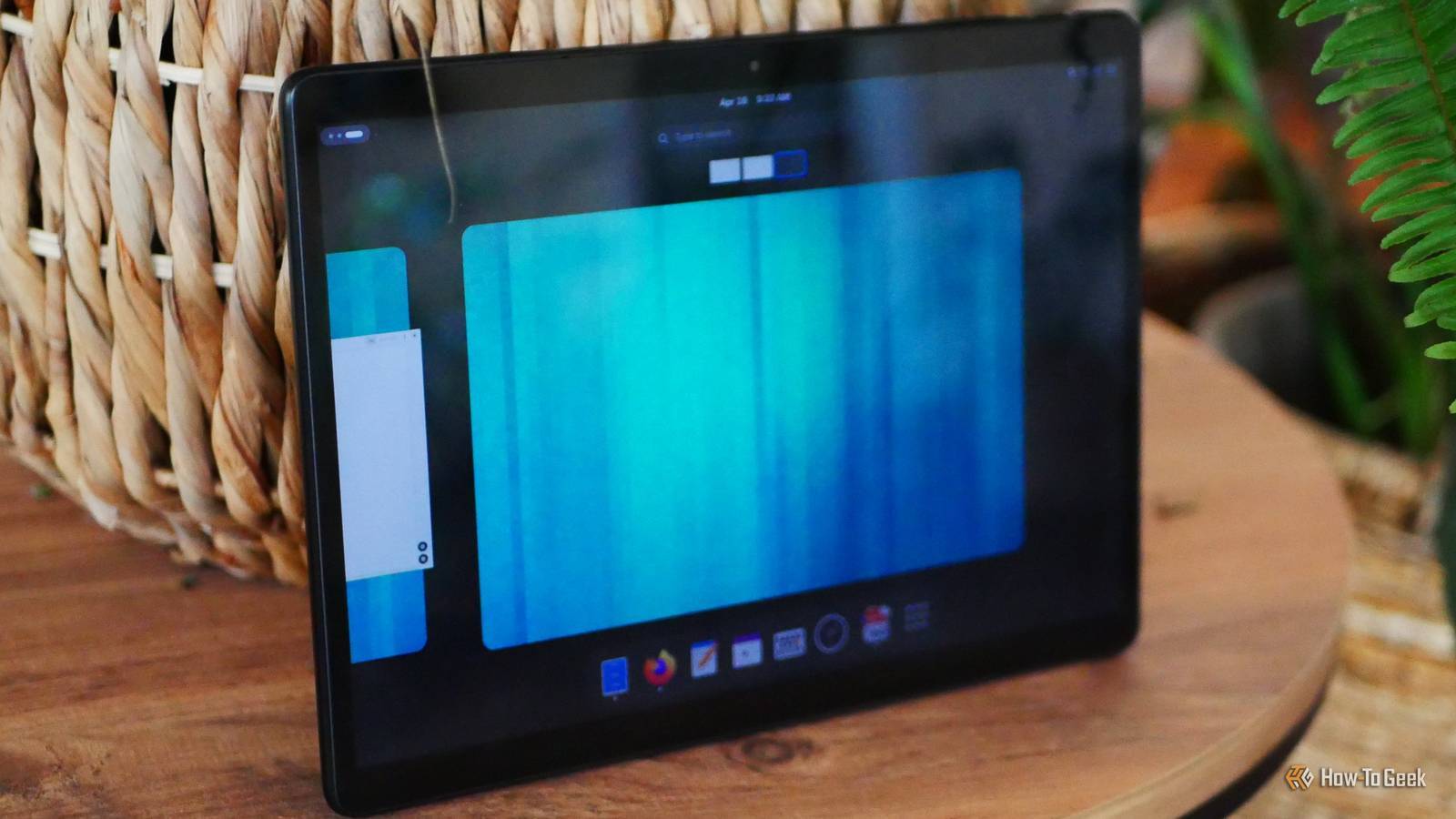
From the moment GNOME 3 launched back in 2011, I felt like it was perfect for a touchscreen, and I’m happy to say that it absolutely is. I’d even go so far as to say that the GNOME interface is a better way to navigate a touchscreen than that of Android or iOS. I’ve said before that I would love to see an official GNOME-only OS, and this experience has only strengthened that desire.
Every aspect of GNOME is easy to tap with a finger. Opening the app drawer and swiping between workspaces feels completely natural with three-finger gestures. Windows are easy to drag around, maximize, or pin to the side. The virtual keyboard that pops up when I tap an input field is the only visual distinction from desktop GNOME. (…)

If you want the OS to boot before it decrypts your drive, why encrypt it in the first place? Honest question, not an attack. For OS to boot without any password it needs to be booting from unencrypted drive. So the attacker could just put their keyloggers on that drive
Yes. Just encrypt /home partition only
This is dangerous. As some data like cache and logs are stored in the root partition. So some of your data from home partition might trickle up the root partition in that form.
My threat model doesn’t include someone gaining direct access to my home desktop. I have Arch Linux with Secure Boot and TPM 2.0 enabled on fully encrypted drive and this chain’s existence makes it easier to know that no one has tampered with my system. On my laptop I am one step further with requirement of BIOS password.
Hence my point about why bother at all. Without full encryption one gets leaks. With full encryption some kind of secret is required. Either password (hence that need of keyboard in earlier comment) or a key, etc
In order to not need a secret during boot, critical parts have to be exposed
Theoretically one could also put logs and cache on encrypted volumes. Maybe that could be some solution. I have in the past had
/var/logson separate partition, so it didn’t make/run out of space. Linux had no issue with that. But that still leaves kernel and OS exposedThe comment I responded to mentioned:
I don’t think you are talking about the same setup and vectors. Their point was to not have fully encrypted drive, so it boots without a prompt
You can achieve this even with full disk encryption with Secure Boot and TPM. That’s how Bitlocker does it. I have this setup on my Desktop — One single root partition with LUKS, Secure Boot on with sbctl and cryptenroll for tpm unlocking. Takes less than 5 mins to setup.
I’ve run into a few reasons:
Generally though I think OS encryption isn’t that important (verification is) vs protecting user data.
I don’t think I’ve heard about some boot-time checksum verification of root partition. Doesn’t mean it does not exist, just that I can’t help here
My point is: if OS is not encrypted, it can be modified. And that verification idea, if is not stored under some encryption, could also be changed. Which means that by the time you put in your password to decrypt your home, you might be already running system that will nullify the protection. Encrypting only your data will only protect you in scenarios when someone snatches your device turned off