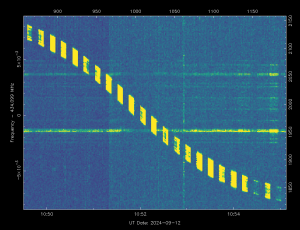
Onno (VK6FLAB)
Anything and everything Amateur Radio and beyond. Heavily into Open Source and SDR, working on a multi band monitor and transmitter.
#geek #nerd #hamradio VK6FLAB #podcaster #australia #ITProfessional #voiceover #opentowork
- 212 Posts
- 541 Comments

 16·1 day ago
16·1 day agoIt appears to me that this globally sustained effort to control the internet and anything connected to it, is a good indication that the
politiciansbillionaires are afraid of theirvoterssubjects.

 1·1 day ago
1·1 day agoWe need this in Esperanto and the lost languages of Lutruwita.

 1·1 day ago
1·1 day agoSo, in UQL?

 1·1 day ago
1·1 day agoYou don’t need to shout!
Also, camelCase:
TurboPascalForLyfe

 2·1 day ago
2·1 day agoNone of your selection criteria describe what you intend to use it for. Graphic art, spreadsheets, video editing, YouTube consumption, word-processing, software development, 3D modelling, whatever.
Each of those has different requirements.
Then there’s the budget which is also a factor.
For some use cases a large 4k TV is excellent, for others you need a $10k budget.
 1·3 days ago
1·3 days agoIn other news, bananas are found to have human-like attributes.

 25·3 days ago
25·3 days agoLet me guess, a European lawmaker had a little chat with Microsoft that went something like this:
Europe: If you don’t allow users to change their search engine, we’re going to break up your monopoly.
Microsoft: Did you know, we’re now offering our users the option to select their preferred search engine on Windows 11.

 24·4 days ago
24·4 days agoUS tech industry cut 123,653 jobs since January 2026, up 66% from last year during the same period — AI now the most cited
reasonexcuse for cuts by US employers: report
My experience with this is receiving emails with “we will not proceed with your application” and absolutely no indication what or why, for positions that I’m uniquely qualified for.
I’m still looking, don’t use Assumed Intelligence, and want to work, but it’s not going well.
I suspect that your needs for human written applications is being thwarted by bots filtering your applicants before you even see them.

 82·5 days ago
82·5 days agoGitHubMicrosoft just switched Copilot to metered billing, and developers are watching months of credits vanish in a single day

 15·6 days ago
15·6 days agoBean counters too stupid to understand Assumed Intelligence bought into the hype and thought that they’d save money. Just like with drugs, the first one is free, now that they’ve fired all the expensive experienced employees, they’re in for a serious amount of hurt, which they’ll pass on to us as “increased operating costs”, which they did to themselves.

 27·6 days ago
27·6 days agoYou are not comparing like for like.
Twitter is pretty much 20 years old, so are Facebook, Reddit and YouTube.
In addition, they were essentially first of a kind in their niche.
The fediverse is not even a teenager and the growth spurt hasn’t set in and may never. In addition, the fediverse is utilitarian by comparison, not much beyond proof of concept. Apps, platforms and instances are fragile and evolving.
Basic things mostly work, but it’s not “cool” enough to tempt organisations to join, media companies, etc.
We barely agree on how things interact with each other, for example, Mastodon uses hashtags, Lemmy doesn’t.
Lemmy has communities, Mastodon doesn’t.
It’s not that one is better than the other, it’s still being worked out by the community.
You also have to remember that there have been many “failures” along the way. Geocities, MySpace, Usenet, AOL, bulletin boards and bang path addressing. The fediverse might succeed, whatever that means, or it might not.
I’m a user on Mastodon, Lemmy and Bluesky, they’re evolving day by day. I’m not sure if I could tell you what I like or dislike about each, they’re just different.

 13·7 days ago
13·7 days agoI suspect that this is about to get very interesting.

 4·7 days ago
4·7 days agoTIL about mosquito dunks

 3·7 days ago
3·7 days agoI would love to read this article, but the number of advertisements on every screen full with a sign-up panel at the bottom make this impossible.





Give it time. My software career is also affected. At the rate they’re spending money at an order of magnitude higher than they’re making. They’ve also all borrowed money from each other. It’s going to collapse in a big heap. Hopefully before it sucks in mum and dad investors.